Some recent popular Home Assistant posts on Reddit revealed that the smart home of someone who lives in Miami Gardens was exposed to the Internet. Other people could turn off the lights and even change the name of their devices. This was all because their MQTT broker was public and unsafe.
Here’s how to make sure you don’t fall victim to the same security issue.

Why smart homes use MQTT
Efficient communication for smart devices
MQTT stands for Message Queue Telemetry Transport. The name may seem confusing, but the concept is quite simple. it’s a lightweight messaging protocol which uses a publish-subscribe model. One device “publishes” messages and another device can “subscribe” to those messages.
For example, a temperature sensor could publish the current temperature every ten minutes. Your smart home software can then subscribe to those messages to know what the current temperature reading is.
The key to this process is the MQTT broker. The broker is responsible for receiving information from the publisher and transmitting it to the corresponding subscribers. The publisher and subscriber do not need to know that the other exists; the MQTT broker takes care of ensuring that messages get where they need to go.
MQTT is ideal for smart homes because it is fast, low-bandwidth, and can run on simple devices such as sensors or smart home microcontrollers. For example, in home assistantYou can use MQTT to allow your Zigbee devices to pass information to your Home Assistant server using Zigbee2MQTT.
How brokers end up exposed on the Internet
Avoid using a public MQTT broker
For your smart home and devices to communicate using MQTT, you need to run an MQTT broker that can take care of the work of routing messages. This is something that should be run locally in your home, so that all communication between your sensors and your smart home happens on your local network.
In the case of the person from Miami Gardens, it seems that instead of creating their own MQTT broker, they were using a public MQTT broker. Since anyone with Internet access could access this broker, other people could send messages to the Miami Gardens smart home from the MQTT broker. With the right commands, anyone could control connected smart home devices, such as turning lights on and off.
There is no real reason why you should use a public MQTT broker for your smart home in most cases. Some guides may mention that they do this for testing purposes, and this may be what the person in Miami Gardens did. It is possible that an AI chatbot regurgitated incorrect information and advised the user to use a public MQTT broker.
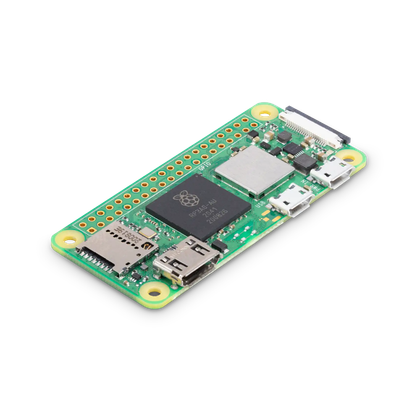
For clarity: don’t do this. You should always run an MQTT broker locally on your own devices. It is incredibly lightweight; you could run an MQTT broker on a Raspberry Pi Zero if you wanted to, so there’s no reason not to organize your own.
- Brand
-
Raspberry Pi
- UPC
-
ARM Cortex-A53 quad-core 64-bit
The Raspberry Pi Zero 2W is super small and super affordable, but has enough computing power for a variety of DIY projects. You can use it to create a portable retro game console, for Klipper/Mainsail, a super compact home or media server, and more.
How to check if your MQTT broker is publicly accessible
Make sure it is local and not exposed.
The quick way to check if your MQTT broker is exposed is to try to access it from outside your home network. You can turn off your Wi-Fi on your phone and use an app like MQTT Explorerpassing it your public IP address and port 1883. If you can connect to your MQTT broker over the cellular network, then your MQTT broker is exposed.
In Home Assistant, verify that your MQTT broker is configured with a local IP address instead of a public web address. Gonna Settings > Devices and servicesopen the MQTT integration and click the three points icon. Select Reconfigure. Make sure Corridor is set to a local IP address or internal hostname, and not an external URL. You should also make sure you have a strong password set.
If you run your own MQTT broker (which is absolutely necessary), then the most likely way you will be exposed outside of your home is because you have set up port forwarding. If you forward port 1883 to your home server, anyone on the Internet can also access it. This can also happen accidentally if you are using functions like Universal Plug and Play (UPnP).
You can see if your MQTT broker is exposed to the outside world using an online service like Shodan and provide your public IP address. It can then allow you to see the services exposed on your public IP. you can too use nmap from the command line with a similar effect.
Block your MQTT broker
Safety is key
If you accidentally expose your MQTT broker and it’s not secure, strangers on the other side of the world may start turning off your lights, or worse. This is why it is important not to allow anonymous connections; the good news is that the MQTT integration in Home Assistant does not support anonymous connections.
Try to avoid port forwarding as well. While port forwarding 1883 can allow you to control the lights remotely, it can also allow other people to do so. There are many other safer options for access Home Assistant remotely. You can improve the security of your MQTT broker by enabling TLS encryption and using port 8883.
Don’t let other people turn off your lights
This is an unusual example, but it shows what can happen if you don’t set up your smart home correctly. Reddit users didn’t do anything more malicious than turning some lights on and off, but bad actors could do much worse.







