The problem, as Hagenah details in the TotalRecall GitHub pageIt’s not about the security around Recall’s database, which he calls “rock solid.” The problem is that once the user has authenticated, the system passes the recovery data to another system process called AIXHost.exeand that The process does not benefit from the same security protections as the rest of Recall.
“The vault is solid,” Hagenah writes. “The delivery truck is not.”
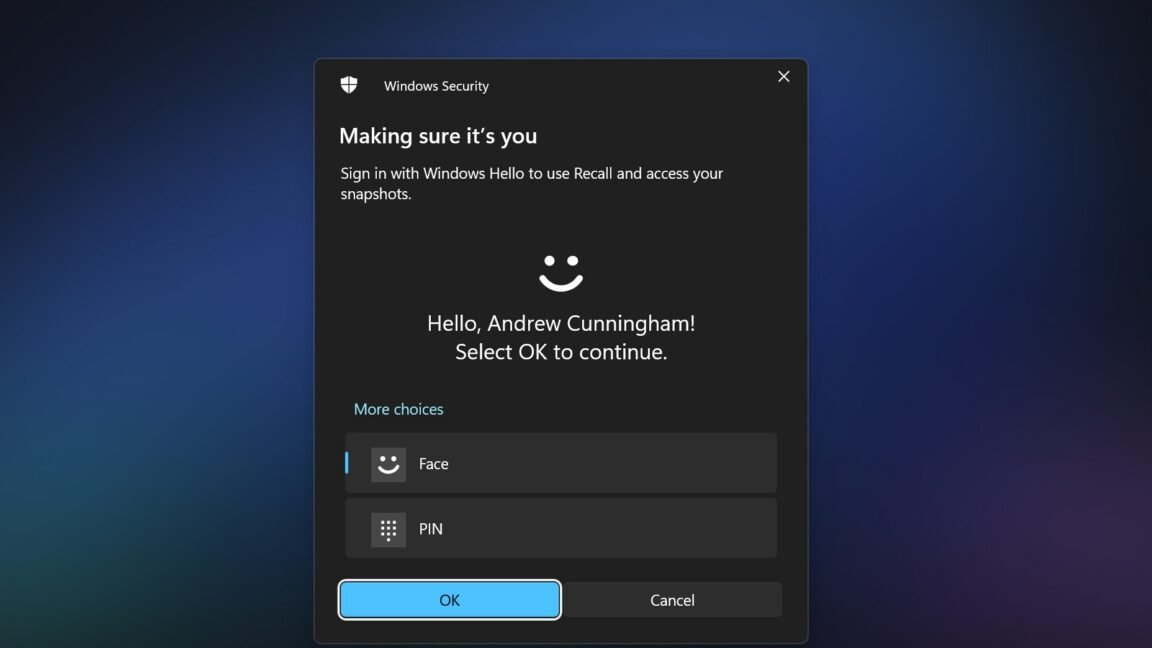
The TotalRecall Reloaded tool uses an executable file to inject a DLL file into AIXHost.exesomething that can be done without administrator privileges. It then waits in the background for the user to open Recall and authenticate using Windows Hello. Once this is done, the tool can intercept screenshots, OCR text, and other metadata that Recall sends to the AIXHost.exe process, which can continue even after the user logs out of their recovery session.
“The VBS enclave won’t decrypt anything without Windows Hello,” Hagenah writes. “The tool doesn’t prevent that. It forces the user to do it, silently accompanies when the user does it or waits for the user to do it.”
Some tasks, including capturing the most recent Recall screenshot, capturing selected metadata about the Recall database, and deleting the user’s entire Recall database, can be performed without Windows Hello authentication.
Once authenticated, Hagenah says The TotalRecall Reloaded tool can access both new information recorded in the Recall database and data that Recall has previously recorded.
Error or not, recovery remains risky
For its part, Microsoft has said that Hagenah’s discovery is not actually a bug and that the company has no plans to fix it. Hagenah originally reported his findings to the Microsoft Security Response Center on March 6, and Microsoft officially classified it as “not a vulnerability” on April 3.