9to5Mac Security Bite is brought to you exclusively by Mosyle, Apple’s only Unified Platform. Everything we do is make Apple devices work-ready and business-safe. Our unique integrated security and management approach combines next-generation, Apple-specific security solutions for fully automated hardening and compliance, next-generation EDR, AI-powered zero trust, and proprietary privilege management with the most powerful and modern Apple MDM on the market. The result is a fully automated Apple Unified Platform, currently trusted by more than 45,000 organizations to get millions of Apple devices up and running effortlessly and at an affordable cost. Request your EXTENDED TEST today and understand why Mosyle is everything you need to work with Apple.
With the release of macOS 26.4Apple is now warning users it believes they are about to paste malicious code into Terminal. The advisory is the latest blow to cybercriminals’ newest and, frankly, most desperate attack vector to get unsuspecting Mac users infected.
In 2023 with the launch of macOS Sonoma, Apple dealt a fatal blow about how malware could bypass your Mac’s built-in protection, Gatekeeper. The update no longer allowed users to right-click and open malicious apps that were not signed or notarized by Apple.
This was a damaging change for cybercriminals who relied on that popular bypass method to infect Macs.
Cybercriminals quickly turned to a new social engineering tactic: tricking users into manually executing malicious commands in Terminal. You’ve probably seen these attacks floating around. I’ve certainly covered my fair share on Security Bite. Downloading a malicious app tells the user to copy a command, open Terminal, and paste it.
It’s rough, but it works. And it’s been working a lot lately.
Basically, the attack bypasses all the layers of protection that Apple has built into macOS. Not even Gatekeeper can save you from yourself. The system sees it as a legitimate user action. You opened Terminal, pasted the command and pressed Enter. As far as macOS is concerned, you intended to do it.
These attacks are typically carried out by downloading malicious applications from fake websites, direct messages, and other delivery methods. Recently, I’ve seen knockoffs of everything from OpenAI’s Atlas browser to Google Chrome. The bar for achieving this is incredibly low, which is exactly why it has become the go-to resource for threat actors who lost their Gatekeeper workaround.
But now it looks like Apple is pushing even harder to protect users.
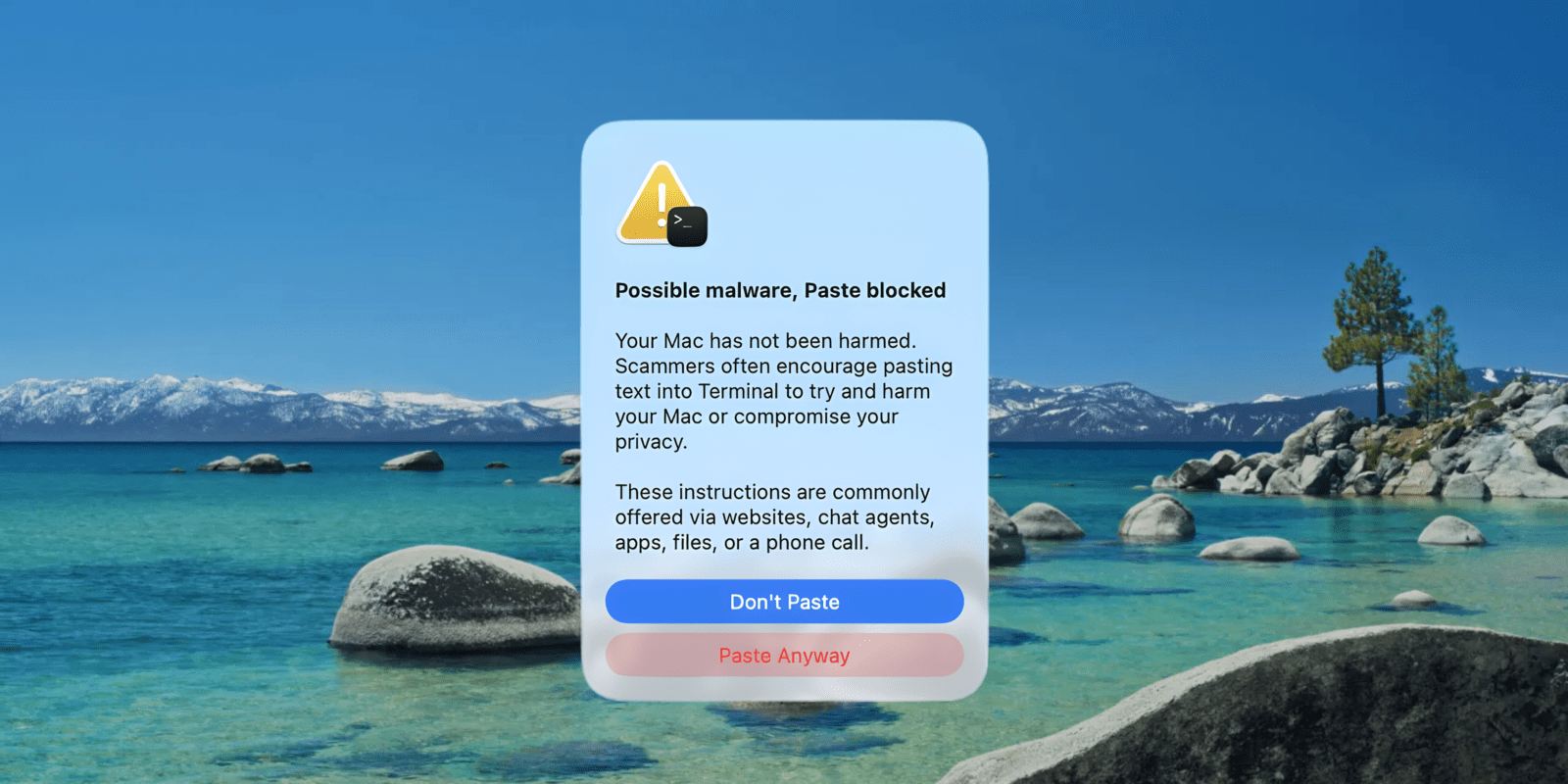
New in macOS Tahoe 26.4, your Mac will now alert you when you paste Terminal commands copied from Safari or other apps, flagging anything that could harm your system. If macOS detects something suspicious, it will display a message before the command is executed, giving you a chance to stop and think before doing something it can’t undo.
Apple is on the offensive again here. It’s a very small, but useful security change that will protect the users who need it most. For someone less Mac savvy who simply followed the instructions of a malicious download, this could be the difference between being safe and being compromised.
Follow Arin Waichulis: LinkedIn, Rags, unknown
Subscribe to 9to5Mac Security Podcast For deep dives and biweekly interviews with Apple’s top researchers and security experts:
FTC: We use automatic affiliate links that generate income. Further.