
Calvin Wankhede / Android Authority
TL;DR
- GrapheneOS has fixed an Android 16 VPN flaw that Google reportedly decided not to fix.
- The bug could allow a malicious app to leak small amounts of data out of an active VPN tunnel.
- In extreme cases, that means it’s possible for Android users to have their IP address leaked, even with strict blocking controls enabled.
A VPN that can leak your location is a pretty big technology failure at the best of times, but it’s especially worrying when Android blocking controls are in place to ensure that won’t happen. that’s the problem GraphenoOS It’s now been addressed in Android 16, with a fix for a VPN bug that Google reportedly decided to leave alone.
As reported by TechnologyRadara security researcher who calls himself lowlevel/Yusuf recently revealed a bug Dubbed Tiny UDP Cannon. The issue affects Android 16 and can allow a regular app to leak a small amount of data out of an active VPN tunnel, potentially exposing your real IP address.
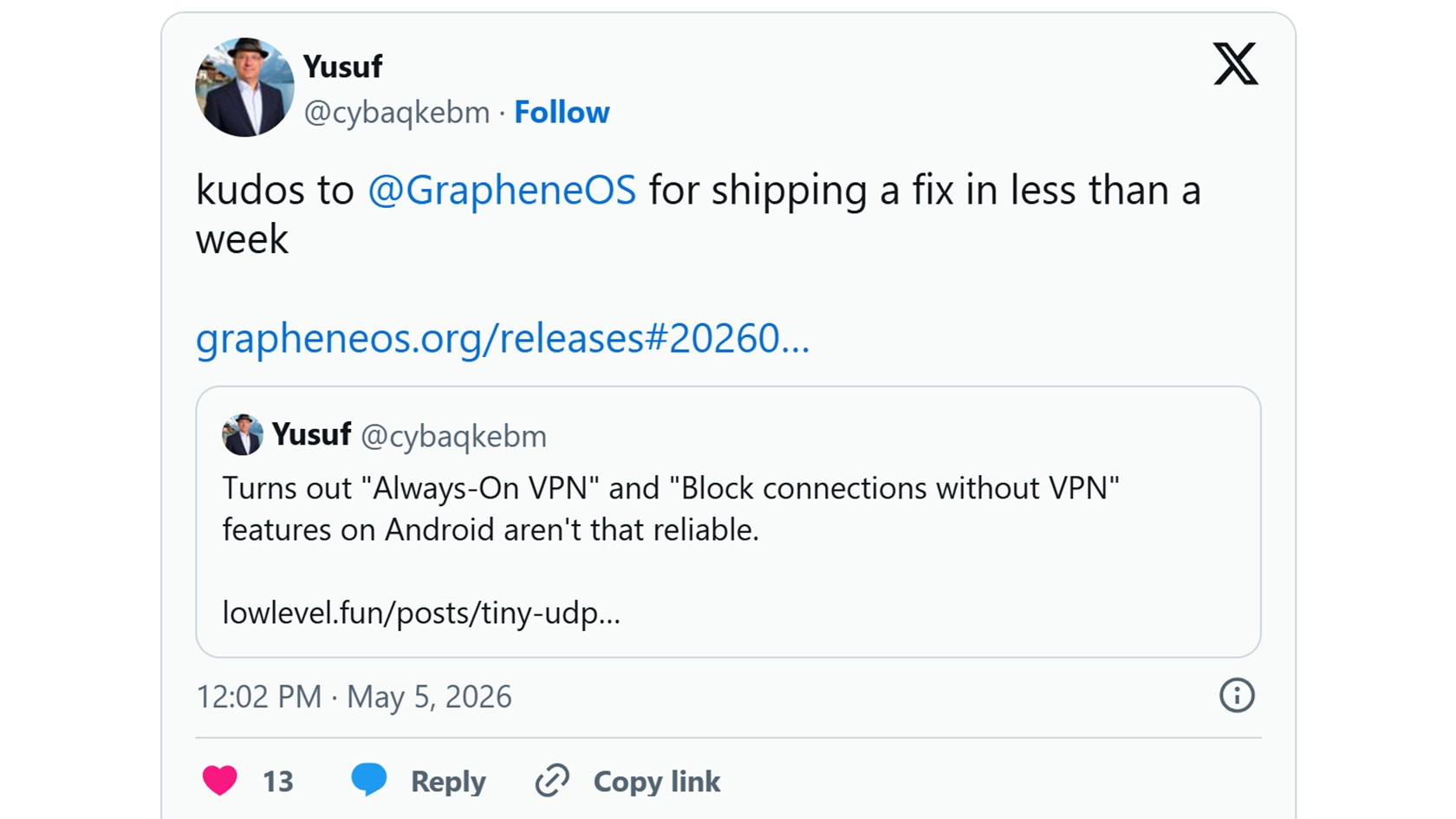
While it’s not a widespread risk, the biggest red flag with the bug is that this can apparently happen even when Android’s strictest VPN settings are enabled. Always-on and blocking VPN connections without VPN are supposed to prevent traffic from leaving your phone unless it goes through the VPN. Its goal is to give you greater peace of mind, but this error creates a narrow path to bypass that protection.
Before you panic, it’s worth noting that an attacker would first need to install a malicious app on your phone to exploit this bug. That makes the daily risk modest for most Android users, but still not ideal if you rely on Android’s VPN blocking mode as a serious privacy guarantee.
The bug appears to be due to a network optimization in Android 16. According to the researcher, Android does not properly check whether the VPN should restrict a small data packet sent when closing certain connections, so it can leave through the normal connection. If the malicious app ensures that the packet contains your IP address, it undermines one of the main reasons why people use VPN in the first place.
Google’s Android security team reportedly classified the issue as “Will not be fixed (unworkable)” and decided that it would not be included in a security bulletin. GrapheneOS, the security-focused, Pixel-focused Android-based operating system, took a different route, completely disabling the underlying feature in release 2026050400.
For GrapheneOS fans, it’s another demonstration that the operating system takes these extreme privacy cases more seriously than its rivals. Android users have no clear official solution at this time, although the researcher notes that the feature can be disabled manually using an ADB command.
Thank you for being part of our community. Read our Comment Policy before publishing.







